For quite some time now, Linux and its derivatives or distros have been the most widely used platform in the cloud. Since many of these Linux instances are headless, i.e. having no graphical user interface (GUI), you need to access them through the command line.
In this post, we’re going to show you how to connect to a Linux EC2 instance via SSH. We’re using a Mac, so some of our screenshots are going to be taken from a Mac UI.
 Source: https://thecloudmarket.com/stats#/by_platform_definition
Source: https://thecloudmarket.com/stats#/by_platform_definition
SSH logins are typically done through public key authentication, which requires users to have their private key on hand. Although you can generate a public-private key pair using a third party tool and then import the public key on Amazon EC2, we are going to go through the usual route which is to generate keys from Amazon EC2 itself. Let me now show you how it’s done.
Generate Keys in Amazon EC2
Sign in to the AWS management console.
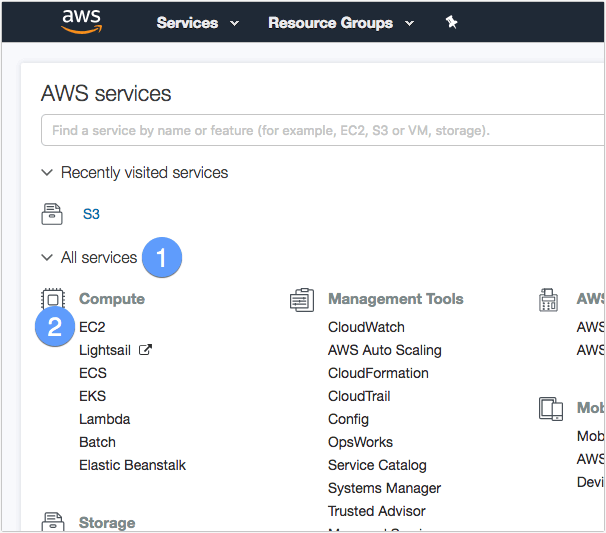
Expand the All Services drop-down and then click EC2 under the Compute section.
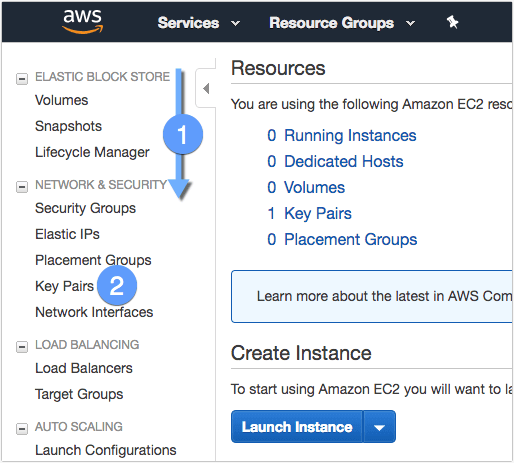
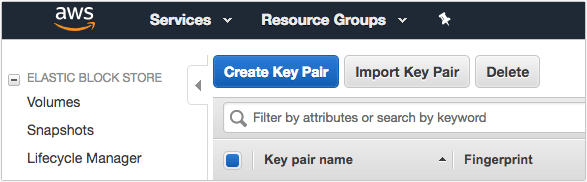
Scroll down the left sidebar until you reach the Network & Security section and then click the Key Pairs menu.
Click the Create Key Pair button.
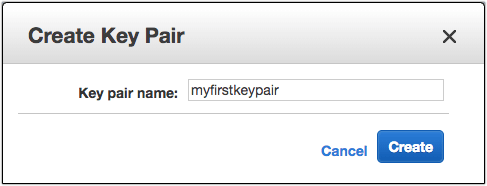
Give the key pair a name and then click the Create button.
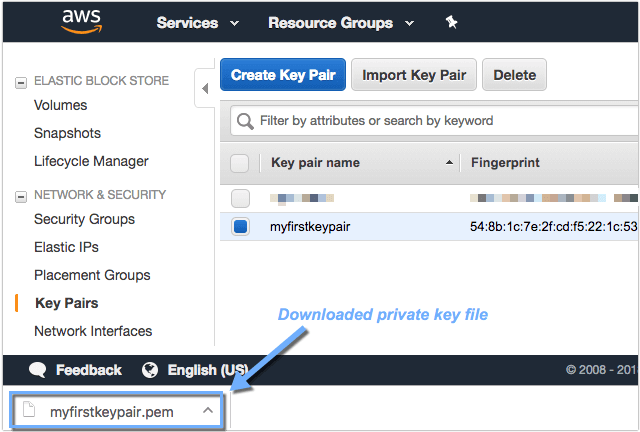
As soon as the key pair is created, its name will be displayed among the list of key pairs and the private key will be automatically downloaded by your browser. Keep that private key file in a safe place and remember where you kept it, as you’ll need it every time you connect to your Linux EC2 instance via SSH.
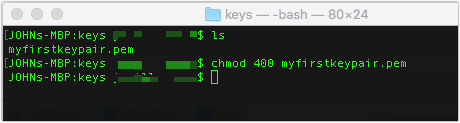
Before you can use that private key file, you’ll need to change its permissions. Launch the Mac terminal from the Dock or launch Mission Control (F4 button) and then go to Other > Terminal.
Navigate to the directory that contains your private key file and then enter:
chmod 400 nameofyourpravatekey.pem
You can now start using your private key to authenticate to your Amazon EC2 Linux instance via SSH.
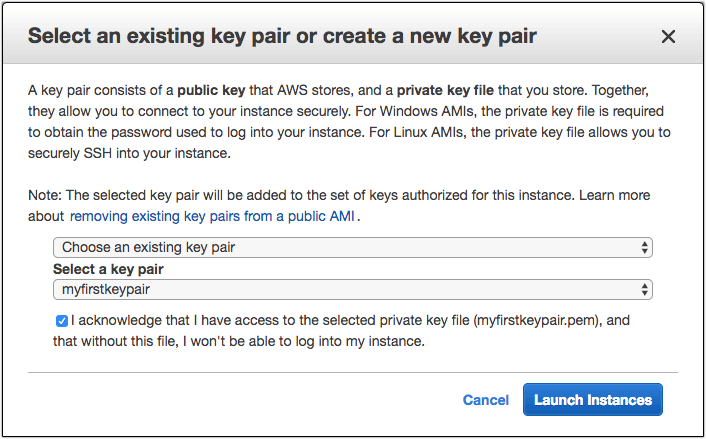
I won’t go into the details of creating a Linux EC2 instance, as that should belong to a separate post, but once you launch such an instance, you need to select the key pair you created so that Amazon EC2 will know what private key file to expect when you connect via SSH.
Once you’ve launched the instance, take note of its Public DNS hostname or Public IP address, as you’ll also be needing either one when you connect via SSH.
To SSH to your EC2 instance from your Mac, just go back to your terminal (or launch it again if you’ve closed it already), navigate into the directory that contains your private key file, and then enter:
ssh -i ./nameofyourprivatekey.pem ec2-user@ipaddress or hostname
For example (this is one line):
ssh -i ./myfirstkeypair.pem ec2-user@ec2-54-88-51-10.compute-1.amazonaws.com
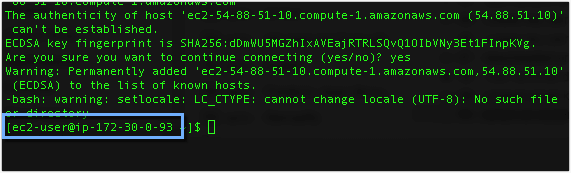
You should then get something like the message below. Just enter ‘yes’.
The authenticity of host 'ec2-54-88-51-10.compute-1.amazonaws.com (54.88.51.10)' can't be established. ECDSA key fingerprint is SHA256:dDmWU5MGZhIxAVEajRTRLSQvQ1OIbVNy3Et1FInpKVg. Are you sure you want to continue connecting (yes/no)? yes
You should then get something like this:
Warning: Permanently added 'ec2-54-88-51-10.compute-1.amazonaws.com,54.88.51.10' (ECDSA) to the list of known hosts. -bash: warning: setlocale: LC_CTYPE: cannot change locale (UTF-8): No such file or directory [ec2-user@ip-172-30-0-93 ~]$
As soon as you see ec2-user@your ec2 instance’s ip address as the prompt, you can start celebrating. You have successfully connected to your Linux EC2 instance via SSH.
Note: One of the common mistakes is selecting the wrong key pair when launching the instance, so make sure the private key you use during SSH login and the key pair you selected prior match. If they don’t match, you would get something like:
Permission denied (publickey,gssapi-keyex,gssapi-with-mic)
We’re done here. See you again next time. Enjoy!